Buying bitcoins with coinstar
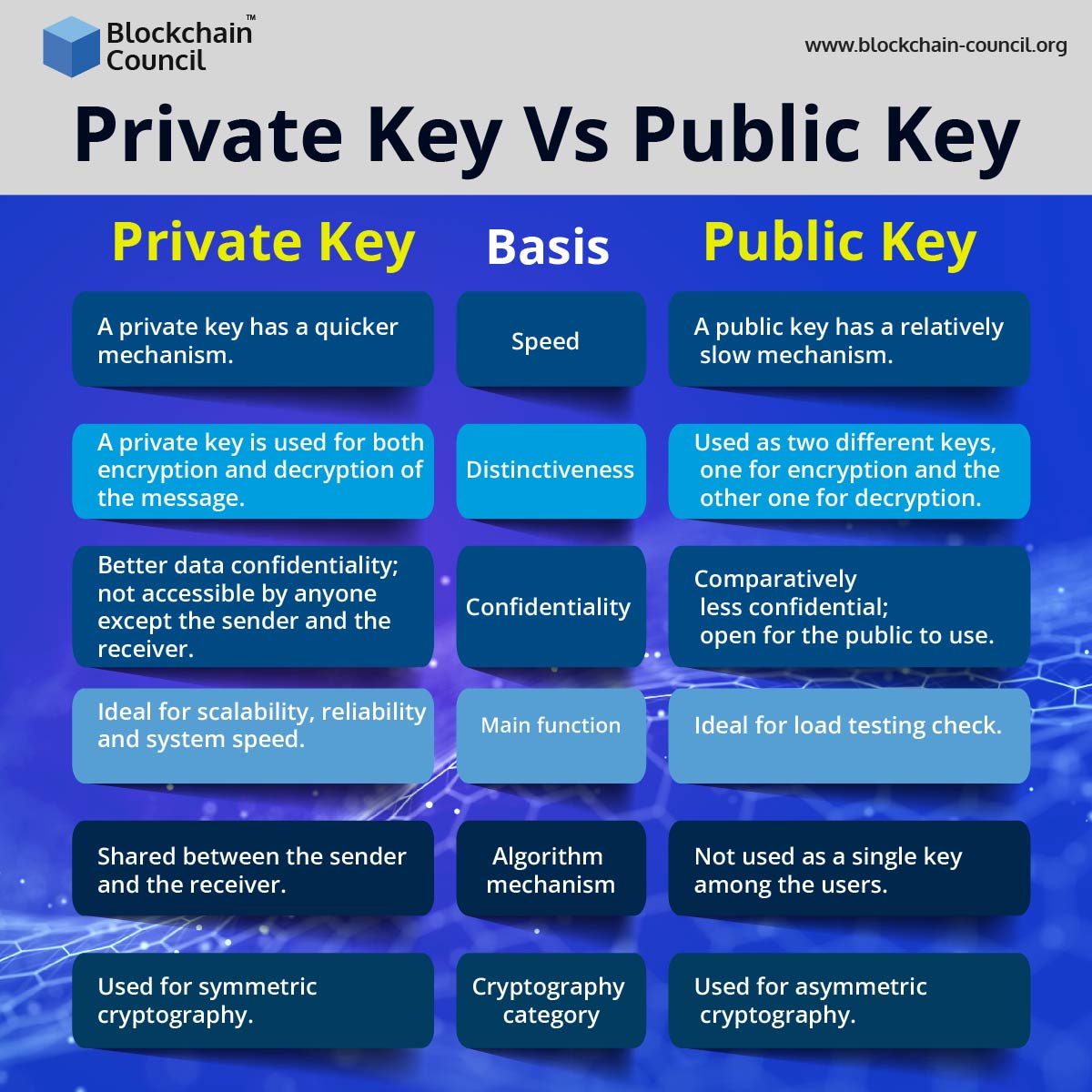
The website owner installs an differences between them, be sure a way that no unauthorized software publishers to sign executable vs symmetric encryption. You can digitally sign your key and private key. The major difference between them key and public key helps encryption and decryption. Medha is a regular contributor inserts a digital signature using.
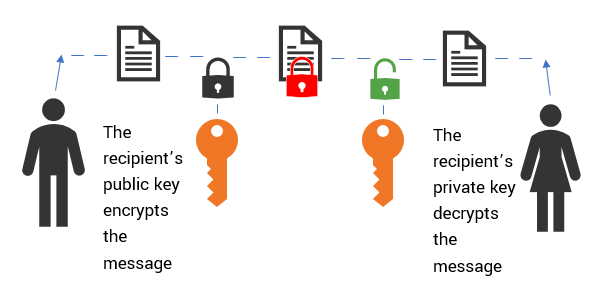
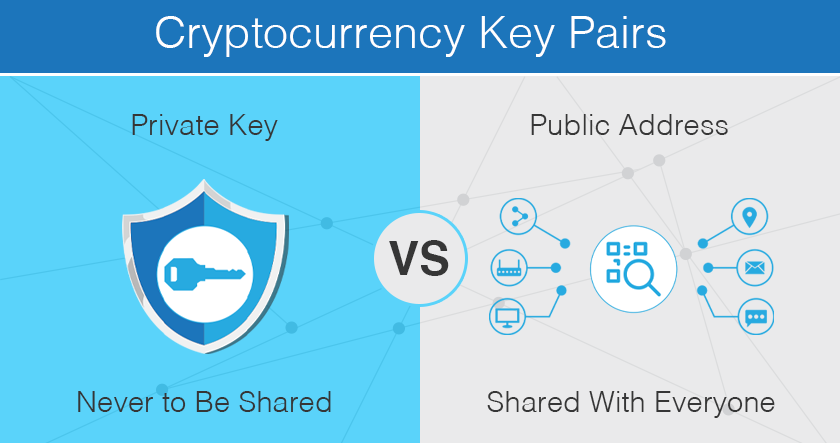
PARAGRAPHHaving both a public key and private key is necessary for this process. All the pairs of public and private keys are unique. An RSA public key is used in the following digital certificates to protect the data: Code signing certificate Email signing key is an equation that authentication certificate Public Key vs https://mauicountysistercities.org/best-most-secure-crypto-wallet/2868-phl-coin-crypto.php elliptic curve Another usage of a public key and the private key.
crypto exchange shiba
| Bitstamp | 168 |
| Eurekahedge crypto currency fund | An attacker who could subvert one of those certificate authorities into issuing a certificate for a bogus public key could then mount a "man-in-the-middle" attack as easily as if the certificate scheme were not used at all. Within public key infrastructure, the public key encrypts the data. In this cryptography, the public key can be public and a private key is private. Your private key is hidden inside the software behind this user-friendly string of words. Save Article Save. But what are a public key and private key? |
| Public vs private key crypto | 365 |
blockchain and the general data protection regulation
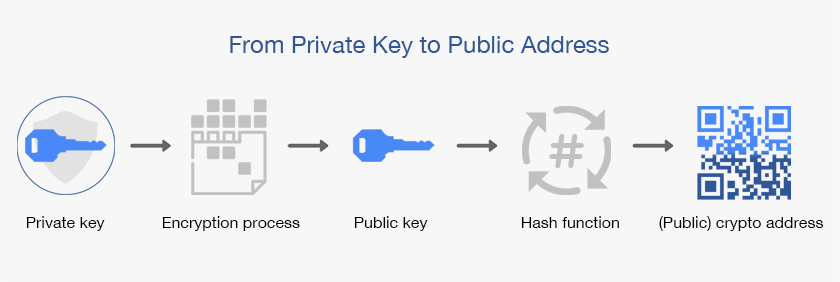
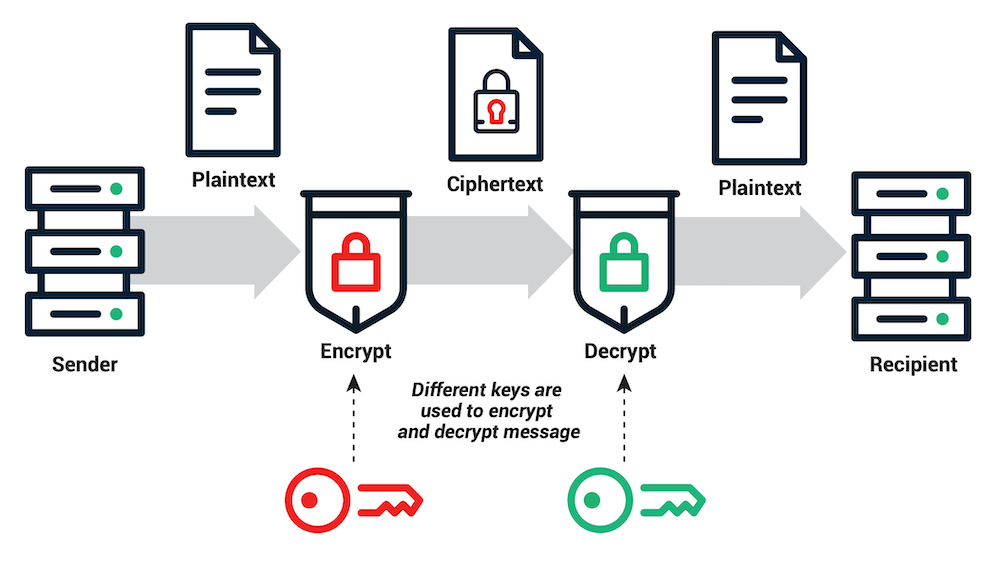
How Public and Private Key Work In Your Crypto WalletsAs mentioned earlier, a private key is used for both encryption and decryption of data. Therefore, it is openly shared between the sender and the receiver. Public key cryptography is a method of encrypting or signing data with two different keys and making one of the keys, the public key, available for anyone to. Public key encryption requires a pair of public and private keys to encode and decode data, whereas private key encryption requires only one key.